Welcome to
Course Cloud
the best place for online learning!
Log In
Sign Up
Don’t have an account yet? Sign Up
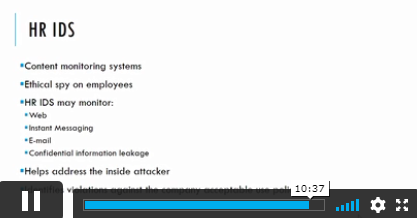
Computer Network Security
What Will I Learn? Introduction to Computer Networks TCP/IP Protocol Suite Computer Networks Security Intrusion Detection and Prevention systems (IDS/IPS) …
230 enrolled on this course
( 50% Off Limited Time )

This Course Includes
- 52 Units
- 1 Year Access
- 8 hours, 8 minutes
- Intermediate
- Accredited Certificate





Frequently asked questions
Can’t find the anwser you’re looking for ? Reach out to customer support team.
As a Lifetime Prime Member, you will receive lifetime access to our entire course library and a student ID card. You will also receive a PDF certificate with every course you complete. Furthermore, you can get unlimited PDF transcripts and 5 hardcopy certificates.
As a Lifetime Prime Member, you will receive lifetime access to our entire course library and a student ID card. You will also receive a PDF certificate with every course you complete. Furthermore, you can get unlimited PDF transcripts and 5 hardcopy certificates.
As a Lifetime Prime Member, you will receive lifetime access to our entire course library and a student ID card. You will also receive a PDF certificate with every course you complete. Furthermore, you can get unlimited PDF transcripts and 5 hardcopy certificates.
As a Lifetime Prime Member, you will receive lifetime access to our entire course library and a student ID card. You will also receive a PDF certificate with every course you complete. Furthermore, you can get unlimited PDF transcripts and 5 hardcopy certificates.


 Get Accredited Certificate
Get Accredited Certificate




 ALL COURSES FOR £49
ALL COURSES FOR £49

